- #ElectionsWithNewsGram
- HOME
- OPINION
- ON GROUND
- INTERVIEW
- IPL 2026
- INDIA
- NewsGram USA
- WORLD
- न्यूजग्राम
- POLITICS
- ENTERTAINMENT
- CULTURE
- LIFESTYLE
- ECONOMY
- SPORTS
- Jobs / Internships
- Misc.
- NewsGram Exclusive
Key Points
ED conducted searches across multiple locations in Bengaluru targeting a cybercrime and money laundering network
Hacker Srikrishna Ramesh is at the centre of the probe with alleged links to the sons of N A Harris
Investigators suspect stolen cryptocurrencies were routed through layered transactions to conceal illicit gains
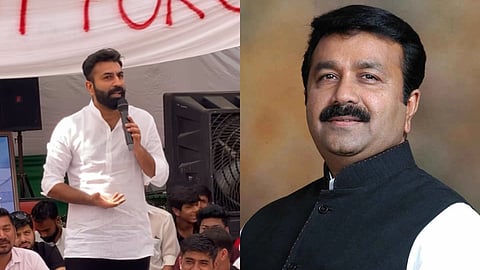
The enforcement directorate (ED) has cracked down on the cyber crime and money laundering network operating in Karnataka, conducting a series of high-profile searches across the capital city in multiple locations. Now, the probe has landed on the doorsteps of a prominent Karnataka politician, N A Harris, the current MLA for the Shantinagar constituency in Bengaluru.
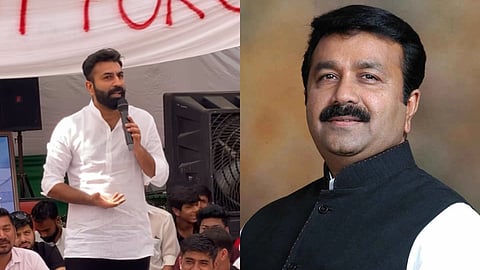
At the centre of the probe is Srikrishna Ramesh alias Sriki, a notorious hacker operating in the cyber city. In addition, Mohammed Haris Nalapad and Omar Farook Nalapad, sons of N A Harris, have also been implicated due to their alleged close connections with Sriki.
ED’s Bengaluru Unit is helming the search operations, and the ongoing investigation has led to the uncovering of a complex web of cyber crime activities, cyber intrusions, and fishy financial transactions meant to conceal illicit gains.
See also: Mumbai cyber fraudsters pose as gas company, siphon off nearly Rs 1 crore in a month
The searches have been well underway since the early hours of Monday morning, 20th April, covering about 12 premises across Karnataka under the Prevention of Money Laundering Act (PMLA) 2002. The agency’s raid also covered Mohammed Haris and Omar Farook’s residence, and it was revealed that both are a direct recipient of the capital gains that the crime garnered.
According to officials, these ED searches have been instigated based upon the multiple First Information Reports (FIRs) and chargesheets filed by the Karnataka Police. They allege the presence of offences such as hacking of domestic and international websites, embezzlement of bitcoins, extortion, and violation of the Narcotic Drugs and Psychotropic Substances (NDPS) Act of 1985.
Officials privy to the investigations have revealed the modus operandi of the cyber crime slash money laundering network. According to the investigating officials, the group allegedly hacked into websites and digital wallets in a bid to steal virtual digital assets (VSAs), which afterwards became the proceeds of the crime. Additionally, sensitive data funds were, reportedly, pilfered in a similar manner via cyber attacks.
"Once the cryptocurrencies were stolen, they were allegedly routed through various crypto trading platforms to obscure their origin. The proceeds were then transferred through multiple bank accounts in a layering process designed to evade detection by authorities. Finally, the laundered funds were purportedly used for personal expenses and benefits by Srikrishna and his associates," the officials have stated.
As the search and probe deepens, further evidence, like digital records and financial statement documents are expected to be uncovered, according to officials. This evidence could yield valuable information about the full extent of the operation and shed light on other accomplices of the network as well.
Suggested reading:
Subscribe to our channels on YouTube and WhatsApp
Download our app on Play Store
